Question 1
Samuel the system administrator has discovered malicious remote connection(s) activities while performing a routine check on his company web server’s log. He had retrieved a Wireshark capture of the malicious network activities for further investigation. Apply the use of Wireshark and assess the given network traffic ICT338 2023 ECA Q1.pcap and answer all the questions below. Explanation and screenshots of the evidence from the Wireshark application must be provided together with the answers.
i. What is the web server’s IP address?
ii. What is the attacker’s IP address?
iii. What technique is attacker using to gain remote access to the victim server? Provide the transport layer protocol and port number used by the attacker for the malicious connection.
iv. What operating system and version is running on the web server?
v. What is the name of the malicious script used by the attacker?
Question 2
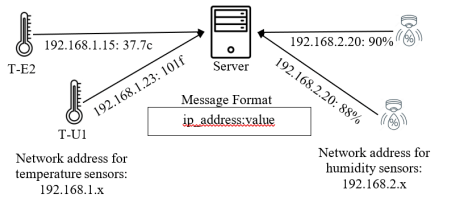
You are working on an IoT pilot project that involves collecting temperature and humidity data from a network of temperature and humidity sensors. There are three types of sensors. Temperature sensor type T-U1, temperature type T-E2, and humidity sensor type H-S1. Temperature sensor type T-U1 measures temperature to the nearest ºF, temperature sensor type T-E2 measures temperature to the nearest 0.1 ºC and humidity sensor H-S1 measures humidity levels to the nearest %. Each sensor sends a message to a central server in the format as shown in the following.
Question 2a
Write a regular expression that can be used to determine the validity of received messages.
Question 2b
Demonstrate the effectiveness of the proposed regular expression using
www.regex101.com or any other regular expression testing tools using appropriate test data. Include screenshots of your testing and provide explanation on the test results.
Question 2c
6 months after the project, it was reported that environmental data was stolen from the network while it is being transmitted from the sensors to the server. The management has decided that encryption of data-in-motion should be implemented. Recommend an encryption type (symmetric or asymmetric) and assess the merits of your recommendation.
